Faraday bags are a necessity today and here’s why you need one. You lock your door to your home or car when you leave to protect your valuables and keep intruders out.
Your devices, like your cell phone, tablet, and laptop contain personal and valuable information that needs to be protected and locked from intruders too.
 Hackers don’t need to physically have your device in order to break into it. Your data can be hacked anywhere you are and you won’t know it until it is too late.
Hackers don’t need to physically have your device in order to break into it. Your data can be hacked anywhere you are and you won’t know it until it is too late.
Your phone, tablet, and other electronic devices are vulnerable to wireless threats, malicious attacks, malware, and tracking.
Faraday bags also protect you by blocking harmful EMF radiation and from your devices.
Best Faraday Bag Buying Guide
Faraday bags come in a range of sizes, for small devices to extra large items like solar panels and generators.
To save you time researching the best options, I have organized my top choices by category to get you the best signal blocking bag for your protection and privacy. This site contains affiliate links. If you buy through them, I may earn a commission at no extra cost to you.
Quick Picks
After testing dozens of Faraday bags across every category, these are the products I actually recommend. Each one has been verified to block signals completely and offers the best combination of performance, durability, and value in its category.
- Phones: Mission Darkness Non-Window 2-Pack
- Key Fobs: Lanpard Key Fob Faraday Cage Protector
- Laptops: Mission Darkness Non-Window Faraday Laptop Bag
- Backpacks: OffGrid by EDEC Backpack
- EMP Protection: Faraday Defense Nest-Z EMP 10 Piece Kit
Top Faraday Bags for Cell Phones
Your cell phone is on you all the time, exposing you to constant EMFs. It also tracks your movements (even in airplane mode) and contains your personal and confidential information.
If you’re going with any shielding product, one for your smartphone is the most important.
1. Silent Pocket Faraday Smartphone Sleeve
 The Silent Pocket sleeve is the on I use every day for my cell phone, so it makes sense it’s my number one recommended product.
The Silent Pocket sleeve is the on I use every day for my cell phone, so it makes sense it’s my number one recommended product.
SLNT uses a patented Silent Pocket Cage technology with multishield. It will block all RF signals (5G and all cellular, WiFi, Bluetooth, RFID, GPs, etc.) from reaching your device.
I have the leather option which looks and feels expensive. You can tell it’s a high quality pouch although looking at it you’d have no idea what it’s capable of. It also comes in a bunch of different colors of nylon.
It fits my phone well (there are two sizes) and doesn’t look like a bulky bag. I like that it has a second pocket to hold my banking and credit cards, protecting them from hacking too.
It’s used by military, Law Enforcement, and other big wigs to protect their handheld devices and technology. That’s a good enough testimonial for me.
Testing it Out – When my cell is in the pouch I cannot get calls, emails, texts etc. My wife tried to find my location and could not. It definitely does what it’s supposed to and gives me peace of mind.
I think it’s the best looking cell phone Faraday bag currently on the market.
2. Mission Darkness Non-Window Faraday Bag
 The Mission Darkness Non-Window Faraday Bag is my second recommendation for shielding smartphones.
The Mission Darkness Non-Window Faraday Bag is my second recommendation for shielding smartphones.
Compared to SLNT’s faraday pouch, it’s much cheaper. I feel it looks cheaper too but it gets the job done and if you’re just putting it in your backpack or bag, who cares, right?
It’s flexible and has a unique serial number. The outer layer is ballistic nylon, making it really durable, water resistant, and abrasion resistant. It should last you a long time.
I have a spare phone stored in one in case of an EMP.
Testing it Out – It comes with a tester app. Definitely no signal penetrated the bag when I tested it or with regular use. I can’t connect a call or pair to Bluetooth.
Cons – I’m not a fan of the velcro closure (SLNT’s is magnetic and I prefer that). I feel it’ll break down faster, it’s loud and just annoying.
Faraday Backpacks
Anti-hacking Backpacks are a great choice for shielding your laptop and tablet. It’s also a really secure option when travelling.
I recommend this type of bag to anyone that uses public transportation or takes their laptop regularly in crowded public places.
1. OffGrid by EDEC Backpack
 OffGrid’s Faraday backpack is my favorite because it looks like a normal backpack, with lots of pockets. It’s really discreet yet inside there are multiple multi-layered shielding pockets, blocking all RF signals.
OffGrid’s Faraday backpack is my favorite because it looks like a normal backpack, with lots of pockets. It’s really discreet yet inside there are multiple multi-layered shielding pockets, blocking all RF signals.
There’s a pocket for your laptop, tablet, mobile device, and a small one for your key fob and cards.
I’m an organized guy. I don’t want everything thrown in to a large pocket, especially my electronics. So this really works for me.
It also has a hardshell case for glasses and a hidden pocket. I really love this bag. It has lots of space but is not bulky or heavy. It’s great for day to day use.
Cons: I wouldn’t recommend this bag for serious off-grid all weather conditions although it does come with a rain cover.
2. Mission Darkness Dry Shield Faraday Backpack
 The top of the line Faraday backpack is the Mission Darkness Dry Shield backpack.
The top of the line Faraday backpack is the Mission Darkness Dry Shield backpack.
This is a serious military-grade tactical backpack. It has a 40L capacity and flexes to hold bulkier electronics and belongings. It is waterproof, dirt proof, soundproof?, snow proof, contaminant proof, and of course signal proof.
With two layers of TitanRF fabric, no communication can penetrate this bag. It protects against data theft, GPS location tracking, and provides you with digital privacy. It also keeps you safe from EMPs and any EMFs from your electronic devices.
This backpack features:
- Adjustable straps and breathable padding for long-term comfort
- Detachable and customizable unshielded MOLLE pouches
- MOLLE Webbing on three sides
- Roll and clip dry bag closure
I love this bag for the superior quality and detail. I also like that you can protect your laptop, tablet, cellphone, key fob, and more all in one hack-proof, track-proof, signal-blocking bag.
3. Silent Pocket Faraday Waterproof Backpack
 The SLNT Faraday backpack is my favorite everyday signal-blocking and EMF-protecting bag.
The SLNT Faraday backpack is my favorite everyday signal-blocking and EMF-protecting bag.
With a sleek, stylish design, no one will realize you have a Faraday cage with Multishield Faraday Shielding technology on your back. It has a 20L capacity, can hold large laptops, tablets, and most electronic devices.
Tested and certified, this technology is MIL‐STD‐188‐125‐2 Compliant, based on Department Of Defense Standard High-Altitude Electromagnetic Pulse Protection Testing. It blocks all wireless signals, giving you digital privacy.
The SLNT backpack features:
- Two closure openings
- Zippered RFID stash pocket
- Duraflex UTX buckles and padded straps
- RF welded seams and high-tension thread
Highly reviewed, and used by Homeland Security, Special Operations, Military, Law Enforcement, and Business Leaders, I’d say it’s a top choice for you to use as well. SLNT also has an entire line of Faraday products, including wallets, laptop sleeves, key cases, bags, etc.
Best Faraday Laptop Bags
Your laptop contains important private and personal information, and for many of us, work documents as well.
You have anti-hacking and malware security on your computer, now it’s time to add an additional layer of security for your laptop.
1. Mission Darkness Non-Window Faraday Laptop Bag
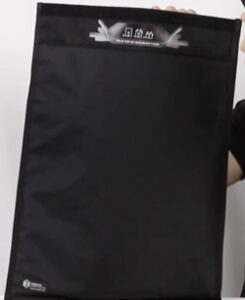 My top recommendation for a wireless signal and radiation-blocking laptop bag is the Mission Darkness Non-Window Faraday Laptop Bag.
My top recommendation for a wireless signal and radiation-blocking laptop bag is the Mission Darkness Non-Window Faraday Laptop Bag.
It is military-grade, like all Mission Darkness products, made for military and law enforcement. Designed with two layers of TitanRF Faraday fabric to block all RF signals (Wifi, Cellular, 5G, Bluetooth, radio, GPS, RFID).
This bag features:
- Universal size to fit extra large laptops (measures 21.5x15x0.1”)
- Transparent pockets on the back
- Secure double roll and velcro closure
- Made of durable, water-resistant ballistic nylon outer layer
- Comes with a serial number for asset tracking
Faraday EMP Kits For Electronics
Here are my recommendations for the best multiple piece Faraday kits
1. Faraday Defense Nest-Z EMP 10 Piece Kit
 The Faraday Defense Nest-Z EMP kits are designed to “nest” smaller Faraday bags into larger ones. You can’t make Faraday material thicker, as it becomes breakable and loses its pliability, which makes it lose its blocking ability.
The Faraday Defense Nest-Z EMP kits are designed to “nest” smaller Faraday bags into larger ones. You can’t make Faraday material thicker, as it becomes breakable and loses its pliability, which makes it lose its blocking ability.
These kits are designed for added protection against EMP or HEMP attacks, giving you multiple metallic layers of Faraday fabric between static electricity devices and your microchip and electronics.
Made of two layers of metal, 5 ply MIL-SPEC Electro-Shielding with a moisture barrier and heavy duty zip lock closure, the bags come in multiple sizes (2 5×7”, 3 8×10”, and 2 12×18”).
I would not use these on their own as a replacement for a Faraday bag. They’re not meant for that. The purpose is to use them in layers to store your electronics devices.
You can also buy Faraday Defense kits in 5 piece, 15, 20, and 40 pieces.
Best Key Fob Anti-Theft Pouch
Pouches for your key fobs are such an inexpensive way to prevent car theft.
Car thieves can wirelessly steal command codes from your key fob from inside your home, pocket, or purse. They transmit that signal to another person waiting near the car, tricking your vehicle into thinking the actual key is there.
This allows them to break in or even steal your car. A simple shielding pouch will block thieves from accessing your vehicle.
1. Lanpard Key Fob Faraday Cage Protector
 With over 24 thousand reviews online, this inexpensive RFID key fob protector will keep your vehicle safe.
With over 24 thousand reviews online, this inexpensive RFID key fob protector will keep your vehicle safe.
It’s small (although available in 3 sizes), blocks all RF signals, and is made of carbon fiber and double military grade RF shielding cloth.
Comes with a lifetime warranty, with 100% satisfaction guaranteed and you get a two pack to protect the keys you use and your spare.
2. Ticonn Anti-Theft Pouch
Ticonn’s pouches comes ![]() in one size. If you have a smaller key, you can also fit your credit card in it.
in one size. If you have a smaller key, you can also fit your credit card in it.
It blocks all RF signals with its double layer of shielding fabric and velcro closure.
This pouch has an inner pocket and outer (unprotected) pocket so you can keep your fob in the pouch and still use your vehicle, as long as it’s in the unprotected part.
You get a lifetime warranty and two pouches.
Although it’s annoying to use at first if you’re used to the convenience of keyless entry, you get used to taking your fob out. Much better than dealing with a stolen car.
3. Faraday Box Set
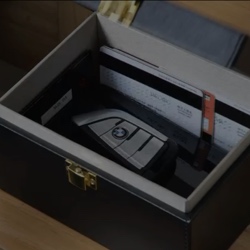 Another option to consider is Samfolk’s RF shielding box set.
Another option to consider is Samfolk’s RF shielding box set.
It comes with a wood and leather box that you can keep on a table by your entry (or anywhere really), giving you a safe space to store all your key fobs, cell phones, and RFID cards.
It also includes two free Faraday pouches for your keys. All items block 100% of RF signals, preventing RFID skimming, key fob signal theft, and wireless cell phone hacking.
This is probably one of my favorite items to gift to people and it really is needed by everyone. Something so easy to use but it provides so much protection.
Frequency Asked Questions
I hope my above recommendations were helpful in finding the right Faraday bag for your needs. I’d also like to share with you the most common questions I get asked regarding these bags and pouches.
What is a Faraday Bag?
Faraday bags (or pouches and sleeves) shield your devices, like your cell phone, key fob, laptop, or tablet, from wireless signals.
This prevents your personal information and banking info from being hacked, tracked, altered or taken.
They also block the radiation from your electronic devices, allow you to be off-grid and protect your electronics if an EMP or CME happens.
The bags come in different sizes to suit your individual needs.
What are the Most Trusted Brands?
High quality Faraday fabric is going to work better, blocking more signals, and it’s going to last longer. Giving you a lot longer life (and value) from your product.
The bags themselves are going to be higher quality too and most of the time the bags just look better too.
Here are my favourite and top recommended brands of RF signal blocking bags. These bags come highly reviewed, are lab tested, and are brands I’ve used personally.
- Silent Pocket
- Mission Darkness
- Shield your body
- DefenderShield
How Does a Faraday Bag Work?
It sounds pretty amazing, doesn’t it? All you have to do is put your smartphone or device into the protected pouch and make sure it’s sealed completely.
So how does this technology work? The bag is lined with a conductive metal mesh that completely enclose a space. This material conducts any electromagnetic fields around the item inside the bag.
It’s essentially a smaller, portable Faraday cage, named after Michael Faraday, a British physicist and chemist. More on him later.
If you were inside a Faraday cage and it was struck by lightning, you would be completely unharmed. Please do NOT try this at home!
While inside your RF shielding bag, your device will not receive or transmit a signal. So your phone won’t get a call, text, email, connect to your Bluetooth speaker, etc.
Although this can be seen as an inconvenience, there are lots of reasons it’s important.
Why Do I Need a Shielding Bag?
This signal blocking technology has so many uses and benefits for you. They provide security, privacy, and health benefits.
Here are just some of the many ways it can help you and why you will want at least one. There are many more I haven’t even listed.
Faraday Bags:
- Prevent hackers and crypto attacks
- Block GPS tracking
- Shield you from electromagnetic field radiation (EMFs)
- Save your electronics in an EMP or CME
- Make it more difficult for large companies to use targeted ads
- Secures your personal and work/business information
- Prevents RFID skimming and cloning
- Prevents car hijacking from intercepted key fob signals
- Prevents warrantless cell phone searches
The security in these bags is needed today more than ever, given how at risk everyone is to cybersecurity attacks and data theft and how much information is on our devices.
It’s better to be safe than sorry.
Who Uses RF Blocking Technology?
This technology is used by military and law enforcement, security professionals, corporate and political leaders. Forensics investigators use Faraday bags to prevent wireless device wiping, of items confiscated and in custody.
Preppers use shielding bags to go off-grid, prevent GPS tracking, and to prepare for EMP attacks. People concerned with EMF radiation use RF shielding bags daily to reduce their exposure to cell phone and other wireless technology emissions.
Faraday cages are used by scientists conducting delicate research that could be affected by electromagnetic radiation.
Do They Block Phone Calls?
Yes, while your cell phone is in the bag, with it properly closed, you will not receive any cellular signals, or Bluetooth, or WiFi. Calls will go directly to voicemail.
My Experience with Faraday Bags
I’ve been using shielding bags now for several years and there’s no way I’d ever travel without one. I’ve had my data hacked, while travelling. I wouldn’t wish it on anyone.
Not only is it stressful, costly, and time consuming, but it also makes you feel exposed and vulnerable. This is why I started using RF-blocking bags in the first place.
I will not travel without one. I’m not going to risk cyberattacks at airports (where you’re more vulnerable) or in another country. This way I know my money (credit cards and debit cards), passport, and cell phone data are safe and secure.
I love my Faraday bags. I use leather SLNT cell phone case every day, while my wife has the new DefenderShield cell phone pouch.
Instead of a diaper bag, I travel with a shielding backpack. It has a Faraday pouch, but I can also put my phone in a regular pocket when I need to be reached.
My laptop contains all my work files. It is incredibly valuable to me, as I’m sure yours is to you. My Faraday laptop bag is a vault for my computer. I keep that thing locked up and secure when it leaves my home.






